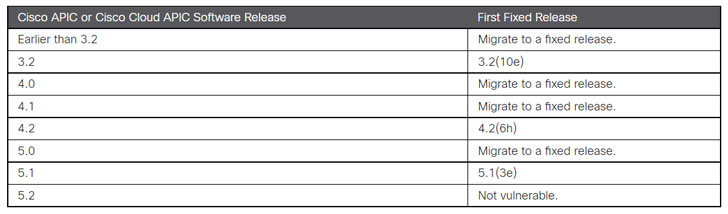
Cisco Systems on Wednesday issued patches to address a critical security vulnerability affecting the Application Policy Infrastructure Controller (APIC) interface used in its Nexus 9000 Series Switches that could be potentially abused to read or write arbitrary files on a vulnerable system.
Tracked as CVE-2021-1577 (CVSS score: 9.1), the issue — which is due to improper access control — could enable an unauthenticated, remote attacker to upload a file to the appliances. ” A successful exploit could allow the attacker to read or write arbitrary files on an affected device,” the company said in an advisory.
The APIC appliance is a centralized, clustered controller that programmatically automates network provisioning and control based on the application requirements and policies across physical and virtual environments.
Cisco said it discovered the vulnerability during internal security testing by the Cisco Advanced Security Initiatives Group (ASIG).
Additionally, the network equipment major said it concluded its investigation into a new BadAlloc flaw in BlackBerry’s QNX real-time operating system, reported on August 17 by the Canadian company. “Cisco has completed its investigation into its product line to determine which products may be affected by this vulnerability. No products are known to be affected,” it noted.
Cisco products that run QNX are listed below –